Historically, passwords alone were used to prove (authenticate) to a system that you are who you say you are. Two-factor and multi-factor authentication (2FA and MFA, respectively) add additional layers of security by requiring a combination of two or more of the following methods to authenticate who you are. The premise underlying MFA is that an unauthorized actor is unlikely to be able to supply all the factors required for access.
- Something you know: certain knowledge only you should know, such as a passphrase, password or PIN - this factor can easily be compromised, hence the need for multiple factors.
- Something you have: any physical object in your possession, such as a hard token (security token, smart card) or soft token (authenticator app, texted codes).
- Something you are: a unique physical characteristic (biometrics), such as fingerprints, retina or iris scan.
We have seen location-based authentication play a part in overall MFA strategies. For example, if you are hard-wired into the corporate network, you may only need one factor (e.g. password), whereas you may need multiple factors if off the network. This can be an acceptable MFA implementation provided access to the office is properly controlled (e.g. with fob access).
When to use MFA
Ideally all accounts should be protected with MFA; the more layers of security between your important information and threat actors, the better. Prioritize MFA implementation on accounts containing key pieces of your identity (personal or financial), accounts protecting high-value data and accounts that are used to access multiple services. MFA should be enabled on any email service - not only do emails typically contain high-value data, but attackers frequently use compromised email accounts to gain access to other accounts through password resets and other social engineering attacks.
The cost and effort required to implement MFA can be high. However, if your organization is compromised, the cost and effort of recuperating from the attack could be higher.
Canadian Centre for Cyber Security
The site 2FA Directory identifies services that support MFA and provides instructions on how to enable MFA for those services.
Limit the number of services that only allow single-factor authentication. If MFA is not available for a particular account, and there is no viable alternative service that offers MFA, then use a sufficiently long passphrase or complex password. However, use of MFA should not be an excuse to use a weak password.
Authentication methods for MFA
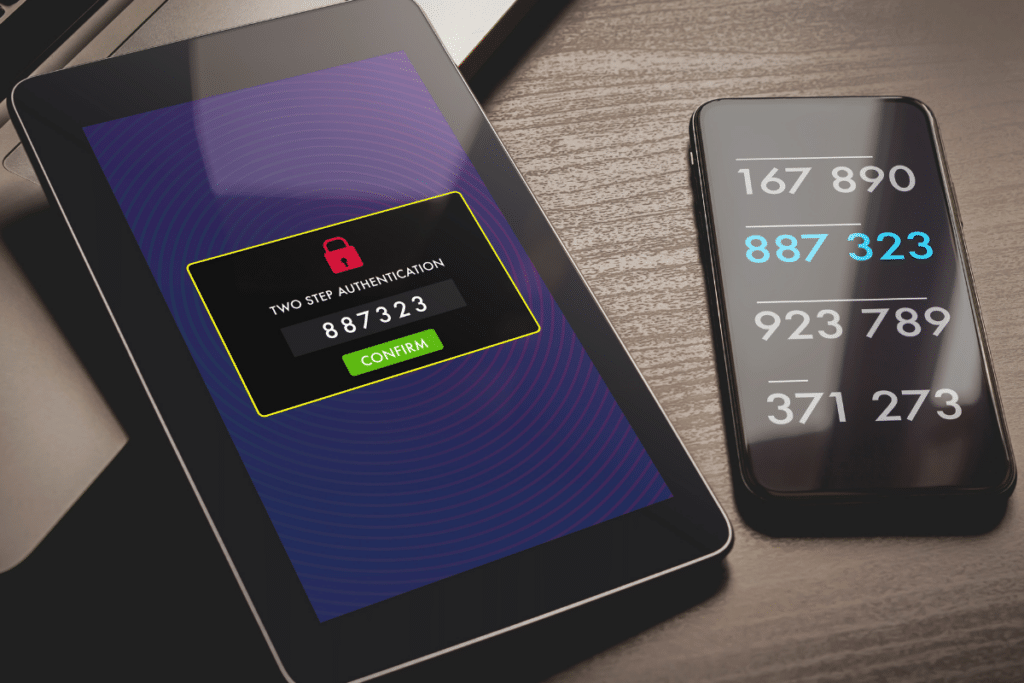
Discussions on 2FA/MFA implementation generally revolve around the "something you have" factor. Popular options include:
Hard tokens
Hardware tokens / security tokens include:
- Disconnected tokens: a device with a built-in screen that produces new codes every few seconds to a minute. The code must be manually entered.
- Connected tokens: a device that is physically connected to the computer to be used, such as a USB token, smart card or RFID tags. Their data is transmitted automatically.
Soft tokens
Software tokens include:
- Authenticator app: a smartphone app - these can either generate codes (called TOTP or time-based one-time password) to be manually entered, or receive push notifications requesting you to accept/decline access to a website or app to verify your identity. TOTP code generators can work entirely offline whereas push-based authenticators must be online to authorize access. Push-based authenticators are also susceptible to a MFA fatigue attack where attackers repeatedly push MFA requests in hopes that you hit "accept" either accidentally or in an (unfortunately misguided) effort to get the notifications to stop.
- SMS verification: a message is sent to a trusted phone number. You are prompted to either interact with the text or use a code provided in the text to verify their identity on a site or app. SMS verification is susceptible to SIM-jacking where an attacker gains access to your cell number, allowing them to receive any codes to your (formerly) trusted number.
Caution when using MFA
Like all cyber security measures, MFA is not failproof.
MFA is still susceptible to social engineering attacks and to information-stealing malware. Never give a MFA code to someone else, never approve sign-in attempts that aren't yours, be wary of phishing attacks, and ensure you follow cybersecurity best practices.
If you are using a hard token, it is possible you could lose it. If you are using a soft token and you lose or change phones or phone numbers, you could lose access if you don't prepare ahead of time. Make sure you have a recovery plan in case of such an event - most services, when setting up MFA, generate one-time use recovery codes. Print these recovery codes and keep them in a safe, secure place.
Implement MFA with Highway 99
Keen on setting up multi-factor authentication but don't know where to start? We can help implement MFA throughout your organization in a way that works for you and your team. Contact us to get started or to learn more about how our managed IT services safeguard your business, digital assets, employees, and customers against cybercriminals.
Get the IT Support Your Business Deserves
"*" indicates required fields